What Does AI OfferHumankind?
Contributors

This article is one of a series on the subject of Artificial Intelligence in mainstream enterprise computing.
Information technology in general and AI in particular serve as assistants to humankind in problem-solving and value creation. Humans can articulate problems and propose solutions beyond their capacity to effectively execute the solution. That is, some solutions require computational capacity that exceeds human capacity in scale, complexity, or both.
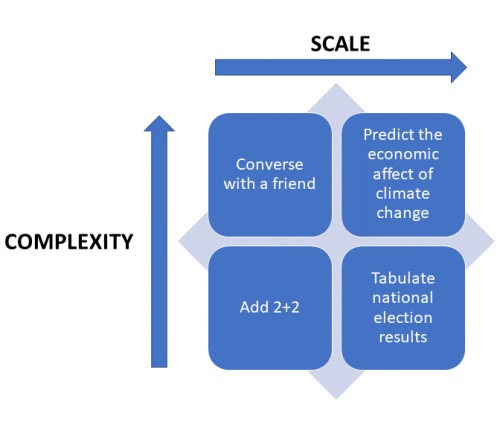
It is important to distinguish between scale and complexity. Humans are more than capable of adding a column of numbers. Machines are better at scale, making short work of calculating totals and averages of thousands or millions of values. Humans are still better than AI at certain kinds of complex tasks when those tasks are performed on a small scale.
Amazon’s Alexa, Apple’s Siri, and Google’s Assistant use a special kind of AI, Natural Language Processing (NLP), to recognize spoken commands and questions, and to provide synthetic replies. As complex as these tasks might be, they are not as complex as human conversation which considers not only words and grammar, but tone, and non-verbal and paraverbal cues. Human conversations take place in multiple simultaneous contexts. Words and grammar mean different things in different conversations. Thus far, NLP allows machines to process language. It does not yet enable them to converse as humans do, bringing feelings, perceptions, and imagination into the exchange of information. On the other hand, humans can converse with only a limited number of other humans at once at a limited pace. On the other hand, a machine’s ability to tirelessly process long streams of natural language, even more than one at a time, is limited only by the technical architecture of the hardware and software on which it is realized.
Figure 1 positions some illustrative problem on axes of scale and complexity. The promise of AI is in the high-complexity, low-scale and high-complexity, high-scale quadrants.
This is what makes widespread applications of AI possible – exponential increases in ubiquitous computing capacity. Computers which filled entire rooms in the 1960s were capable of little more than arithmetic at scale. Today, billions of mobile phones contain the computing capacity required to perform the complex tasks which we refer to as Artificial Intelligence. Except where human “wiring” remains the better tool for some kinds of problem-solving, machines can outperform humans in both scale and complexity. This may seem obvious, but it is exactly the point of all technology. The first sharpened stone was a better cutting instrument than human fingernails. This is what we humans do. We are toolmakers. We create things that allow us to solve problems and create value better, faster, and more reliably than we can with our innate capacities. AI is just a new tool. It may be an exceptionally interesting tool because, more than a sharpened stone, we see a bit of ourselves reflected in it.
Portions of this article originally appeared in the Journal of the World Complexity Science Academy Volume 1, Issue 2 as “Artificial Intelligence in Mainstrem Enterprise Applications”, Picirillo, D. 2020.https://www.wcsaglobal.org/volume-1-issue-2-2020
- AI In Mainstream Enterprise Applications
- What does AI offer humankind?
- What Does AI Offer Users Of Mainstream Enterprise Systems?
Other Popular Articles
In the digital age, businesses must adopt an ad
GRC is the capability, or integrated collection