What Is Penetration Testing? A 2026 Expert Guide
Contributors

Penetration testing is a crucial element of modern cybersecurity. As we move through 2026, organizations are increasingly recognizing that relying solely on traditional defenses, such as firewalls and endpoint protection, is inadequate. Penetration testing identifies vulnerabilities proactively, preventing exploitation by malicious actors and offering essential insights to strengthen the overall security posture.
Who should read this? Security leaders, IT teams, and DevOps engineers looking to elevate cyber defenses in 2026.
What is Penetration Testing?
Penetration testing involves ethical hackers systematically simulating cyberattacks on an organization's applications, networks, or infrastructure. Unlike automated vulnerability scans, penetration tests are meticulously manual, precise, and driven by specific security goals. They validate defense mechanisms, enhance incident response capabilities, support organizations in meeting stringent compliance standards, including PCI DSS, HIPAA, SOC 2, and ISO 27001.
Learn More:
OWASP Web Security Testing Guide
NIST SP 800‑115 “Technical Guide to Information Security Testing"
Essential Penetration Testing Methodology (6 Phases)
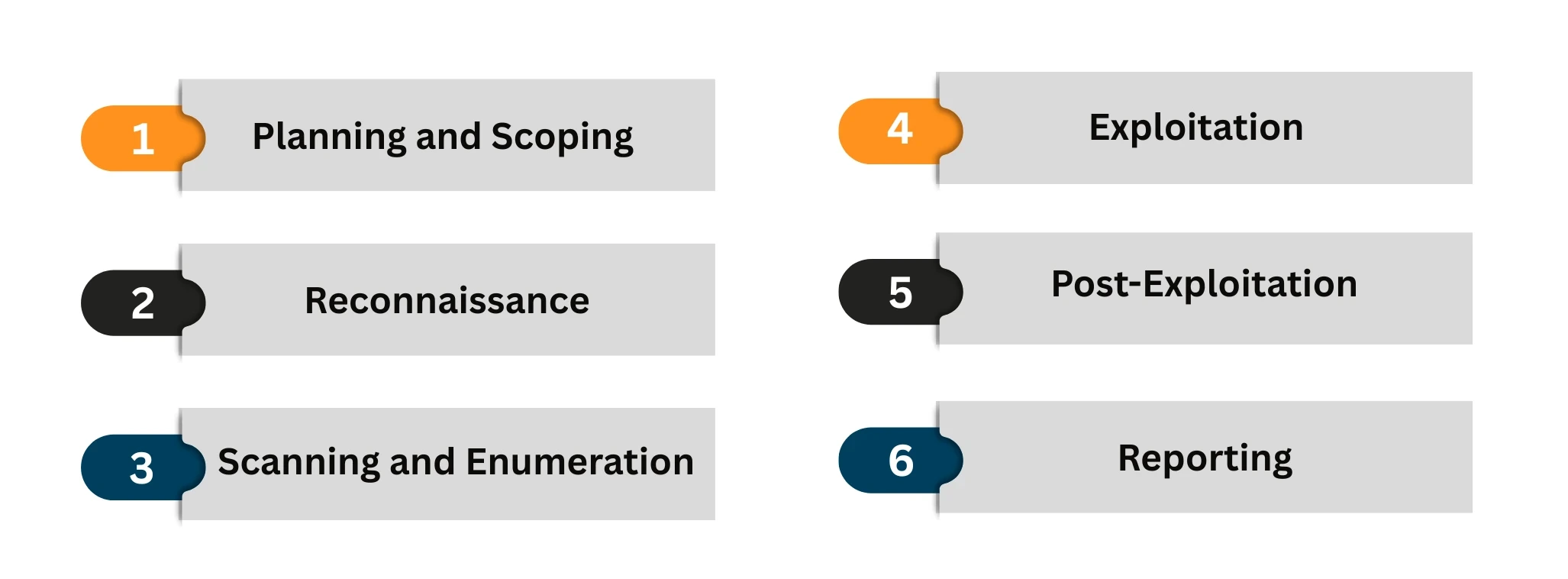
- Planning and Scoping: Clearly define the test scope, objectives, compliance requirements, and legal boundaries to ensure a comprehensive understanding of the project. Proper planning ensures that all critical systems, assets, and business priorities align with the testing process, avoiding potential operational disruptions.
- Reconnaissance: Gather public information and passively identify potential vulnerabilities using tools like WHOIS lookups, DNS enumeration, and monitoring exposed services. This phase mimics the initial intelligence gathering by real-world attackers.
- Scanning and Enumeration: Use automated tools to identify live hosts, open ports, services, and system versions. Enumeration digs deeper, discovering usernames, file shares, and other critical points of potential entry.
- Exploitation: Safely exploit identified vulnerabilities, such as software flaws or misconfigurations, to verify if unauthorized access is achievable. This phase closely replicates actual attack scenarios without impacting operational stability.
- Post-Exploitation: Determine the potential impact and assess how attackers could escalate privileges, pivot across systems, or access sensitive data. This stage assesses the possible depth of compromise.
- Reporting: Document findings comprehensively, providing visual proof, risk severity ratings, impacted assets, and clear, actionable remediation recommendations.
Most penetration tests fail before they even start because the planning was wrong.
Get the Pen Testing Planning Checklist
Penetration Testing Models Explained
- Black Box Testing: Testers simulate external threats without prior knowledge of the system's internal workings. Ideal for evaluating external defenses and identifying perimeter vulnerabilities.
- White Box Testing: Offers testers complete visibility into the system, including source code and configurations. Optimal for deep audits, secure coding assessments, and identifying complex internal vulnerabilities.
- Grey Box Testing: This approach provides testers with limited knowledge, effectively simulating insider threats or partially informed attackers, and is valuable for testing privilege escalation scenarios.
Internal vs External Pen Testing
| Aspect | Internal Pen Testing | External Pen Testing |
| Objective | Simulate insider threat | Simulate external attacker |
| Starting Position | Attacker already inside | Attacker outside perimeter |
| Focus | Lateral movement, privilege escalation | Perimeter breach, initial access |
| Key Targets | AD, internal apps, servers | Websites, VPN, APIs, email |
| Techniques | Credential abuse, AD exploitation | Port scan, DNS abuse, OWASP attacks |
| Cloud Scope | Internal cloud workloads | Public cloud exposure |
| Compliance Fit | ISO 27001, HIPAA | SOC 2, PCI-DSS, GDPR |
| Main Outcome | Impact after breach | Exposure before breach |
| Best For | Zero-trust validation | SaaS, remote-first firms |
Specialized Penetration Testing Domains
- Network Penetration Testing: Evaluates the resilience of network devices (routers, firewalls, switches) against lateral movement, unauthorized access, and configuration errors.
- Web Application Penetration Testing: Identifies web-specific vulnerabilities, including SQL injection (SQLi), Cross-Site Scripting (XSS), and Cross-Site Request Forgery (CSRF), aligning with the OWASP Top 10 vulnerabilities.
- Wireless Penetration Testing: Tests wireless network infrastructure for rogue access points, weak encryption, and insecure configurations, essential for securing remote work and BYOD environments.
- Social Engineering Testing: Evaluates the human factor in cybersecurity through phishing, impersonation, and baiting exercises, critically assessing the effectiveness of organizational training.
- IoT and Cloud Security Testing: Analyzes vulnerabilities in smart devices and cloud services, identifying misconfigurations, API vulnerabilities, and firmware weaknesses.
Strategic Advantages of Penetration Testing
- Identifies real-world exploitable vulnerabilities proactively.
- Validates the effectiveness of existing security measures.
- Ensures compliance with key industry standards.
- Enhances incident detection, response, and recovery processes.
- Strengthens organizational credibility with customers and stakeholders.
The Role of AI and Continuous Testing in 2026
As artificial intelligence accelerates the pace of cyber threats, organizations must adopt continuous penetration testing, integrating it seamlessly within their CI/CD pipelines. Regular automated vulnerability scans should be supplemented with expert-led penetration tests, providing the necessary depth and critical oversight to counter advanced threats.
Penetration Testing as a Service (PTaaS)
PTaaS is a modern, on-demand approach to penetration testing that combines traditional ethical hacking with continuous delivery via a secure platform. It's ideal for organizations that require scalable, flexible, and always-on security validation, particularly those with rapidly changing infrastructures, CI/CD pipelines, or compliance needs such as SOC 2, ISO 27001, or PCI-DSS. Benefits of Ptaas include:
- Immediate retesting capabilities post-remediation.
- Seamless integration within development and operational workflows.
- Access to expert remediation guidance and continuous support.
Organizations adopting PTaaS are better positioned to rapidly respond to emerging threats, thereby maintaining robust and proactive cybersecurity measures.
Conclusion: Building Resilient Security in 2026
In 2026, resilience means more than just defense; it means proactive validation, compliance assurance, and stakeholder confidence. Organizations that integrate penetration testing into their broader security and DevSecOps strategies will be best positioned to adapt, recover, and thrive in the face of evolving cyber risks.
Other Popular Articles
In the digital age, businesses must adopt an ad
GRC is the capability, or integrated collection