How to Perform a Successful Network Penetration Test: Comprehensive Guide for 2025
Contributors

Cyber threats are becoming increasingly sophisticated, underscoring the need for proactive measures such as network penetration testing. This comprehensive guide provides cybersecurity professionals, IT leaders, and compliance managers with detailed insights to identify vulnerabilities, mitigate risks, and enhance their cybersecurity defenses.
What is Network Penetration Testing?
Network penetration testing is a cybersecurity practice that simulates cyberattacks on an organization’s network. The goal is to identify security weaknesses before malicious actors can exploit them. Regular penetration testing is essential for validating existing security controls, uncovering hidden vulnerabilities, and ensuring compliance with regulations such as HIPAA, PCI-DSS, and SOC 2.
Types of Network Penetration Testing
- Internal Testing: This approach simulates insider threats to identify vulnerabilities that employees or compromised accounts could exploit. It also uncovers weaknesses in privilege management, internal network segmentation, and the handling of sensitive data.
- External Testing: This testing assesses protection against external internet threats by targeting web servers, VPNs, and other publicly accessible services. It verifies the effectiveness of perimeter security measures like firewall configurations, intrusion detection systems, and external authentication methods.
- Black Box Testing: Black Box Testing simulates attacks by testers who have no prior knowledge of the network, replicating realistic external cyber threats. It evaluates how effectively an organization can detect and respond to unknown or unexpected cyberattacks.
- White Box Testing: White Box Testing involves testers with complete knowledge of the network, enabling a detailed analysis of system vulnerabilities and configurations, including security controls, code quality, and infrastructure setups. It is typically used during system development and deployment phases, offering insights into potential weaknesses within the architecture.
- Grey Box Testing: It combines elements of Black Box and White Box testing, giving testers partial knowledge that mimics insider threats. It helps identify security flaws resulting from limited knowledge or restricted access. This method is primarily useful for assessing complex attack scenarios that involve both external and internal threat vectors.
Top Network Security Threats in 2026
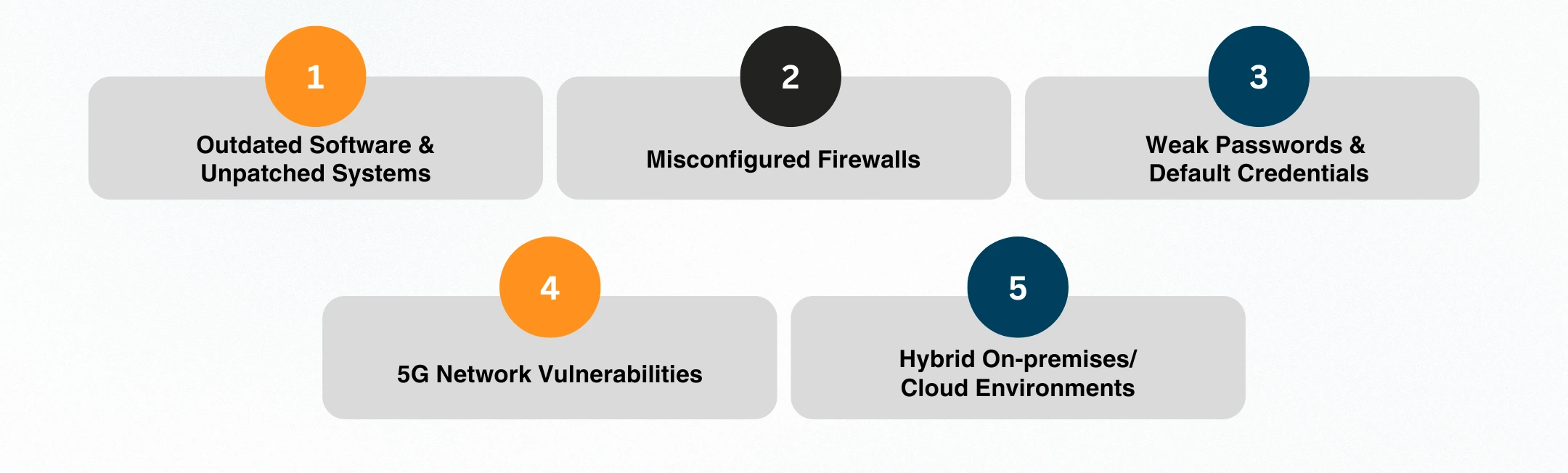
- Outdated Software and Unpatched Systems: Cybercriminals continue to exploit unpatched vulnerabilities, significantly contributing to ransomware incidents through remote code execution (RCE). The Equifax breach highlights the devastating impact of unaddressed software vulnerabilities.
- Misconfigured Firewalls: Firewall misconfigurations inadvertently grant attackers access to critical network segments. A prominent example was the 2023 breach of a major university, which allowed attackers to gain complete control over internal finance and HR systems.
- Weak Passwords & Default Credentials: Weak or default credentials remain prevalent, causing over 82% of breaches according to Verizon’s recent Data Breach Investigations Report. Routinely updating and enforcing strong credential policies is a critical countermeasure.
- 5G Network Vulnerabilities: Expanding 5G deployments introduce new risks, such as data interception and unauthorized access via edge computing nodes and IoT devices. Vigilant security practices for these emerging technologies are paramount.
- Hybrid On-premises/Cloud Environments: Hybrid infrastructures are becoming increasingly common, offering attackers new pathways for lateral movement between cloud and on-premises resources due to misconfigurations and weak security boundaries.
Essential Tools for Effective Network Penetration Testing
- Nmap: Essential for initial network discovery, service enumeration, and port scanning.
- Nessus: Critical for comprehensive vulnerability scanning, identifying known CVEs, and compliance issues.
- Metasploit enables testers to conduct realistic exploit simulations and validate the severity of vulnerabilities.
- Wireshark provides detailed, real-time analysis of network traffic, facilitating a deep inspection of packet-level data.
- Burp Suite: Ideal for examining web application vulnerabilities within network environments, including testing APIs and service interfaces.
Step-by-Step Guide to Network Penetration Testing

- Scope Definition: Clearly outline the test boundaries, target systems, compliance goals, and operational constraints to secure formal stakeholder authorization.
- Reconnaissance: Conduct passive reconnaissance (using WHOIS, DNS, and Shodan) to gather publicly accessible data. Utilize active reconnaissance tools, such as Nmap, for detailed service mapping and enumeration.
- Vulnerability Scanning: Use Nessus to systematically scan and identify vulnerabilities, prioritizing them by severity and potential impact on critical assets.
- Exploitation: Safely execute exploits using Metasploit, validating the actual risk associated with identified vulnerabilities. Document findings comprehensively, maintaining minimal operational disruption.
- Post-Exploitation: Evaluate potential risks further, including lateral movement, privilege escalation, and data exfiltration. Utilize frameworks like MITRE ATT&CK and CVSS to provide structured, actionable insights.
- Detailed Reporting and Actionable Recommendations: Compile comprehensive reports including executive summaries, technical documentation, and visual evidence. Emphasize clear, actionable remediation steps and suggest follow-up retesting.
Best Practices for Network Penetration Testing
Here is what separates a thorough test from a false sense of security.
- Obtain explicit formal authorization with defined testing scope and hours.
- Integrate manual testing alongside automated scanning tools.
- Maintain thorough documentation throughout all testing phases.
- Conduct penetration testing in controlled environments to minimize production impact.
Common Pitfalls to Avoid
Here are the mistakes that turn a good pentest into a missed opportunity.
- Ignoring insider threats and lateral movement possibilities.
- Excessive dependence on automated tools without manual validation.
- Neglecting retesting post-remediation.
- Insufficient communication potentially leads to unnecessary operational downtime.
Conclusion
Effective network penetration testing remains a crucial part of cybersecurity strategies in 2026. Organizations that understand the changing threat landscape, adopt suitable testing techniques, and follow best practices are much better equipped to protect sensitive data, stay compliant with regulations, and reduce overall cyber risks.
Other Popular Articles
In the digital age, businesses must adopt an ad
GRC is the capability, or integrated collection