Mobile App Pen Testing Guide 2026 - OWASP, CI/CD Methods, [Tools + Checklist]
Contributors

Recently, the mobile app risk profile has changed. New regulations like PCI DSS v4.0 mandate stronger testing by March, while healthcare and data-driven apps face heightened oversight on SDKs and tracking. Attackers are shifting to APIs and supply chains, exploiting incidents like CocoaPods flaws, while millions of devices still run outdated operating systems, leaving known holes wide open.
The bottom line is that annual audits no longer cut it. To safeguard compliance, protect revenue streams, and maintain customer trust, organizations must adopt continuous, release-aligned mobile penetration testing as a core security control.
Let us understand every aspect of mobile application penetration testing.
OWASP Mobile Top 10 Overview (2026 Edition)
Understanding the OWASP Mobile Top 10 is foundational to any mobile pen test. Here is a breakdown of the most critical risks:
| Risk | Real-World Mobile Example |
|---|---|
| Improper Platform Usage | Misuse of Android intents or iOS Keychain leading to data leakage. |
| Insecure Data Storage | Banking app stored PINs in an unencrypted SQLite DB. |
| Insecure Communication | Health apps sending PHI over HTTP without TLS. |
| Insecure Authentication | Biometric fallback to a weak PIN without server validation. |
| Insufficient Cryptography | Use of MD5 to hash sensitive tokens. |
| Insecure Authorization | Normal user accessing admin-only app functions. |
| Client Code Quality | Unhandled exceptions reveal sensitive logs. |
| Code Tampering | Repackaged Android APK distributed with injected adware. |
| Reverse Engineering | Decompiled app reveals embedded API keys. |
| Extraneous Functionality | Debug endpoints left active in the production app. |
Source: OWASP Mobile Top 10
Step-by-Step Methodology for Mobile Penetration Testing
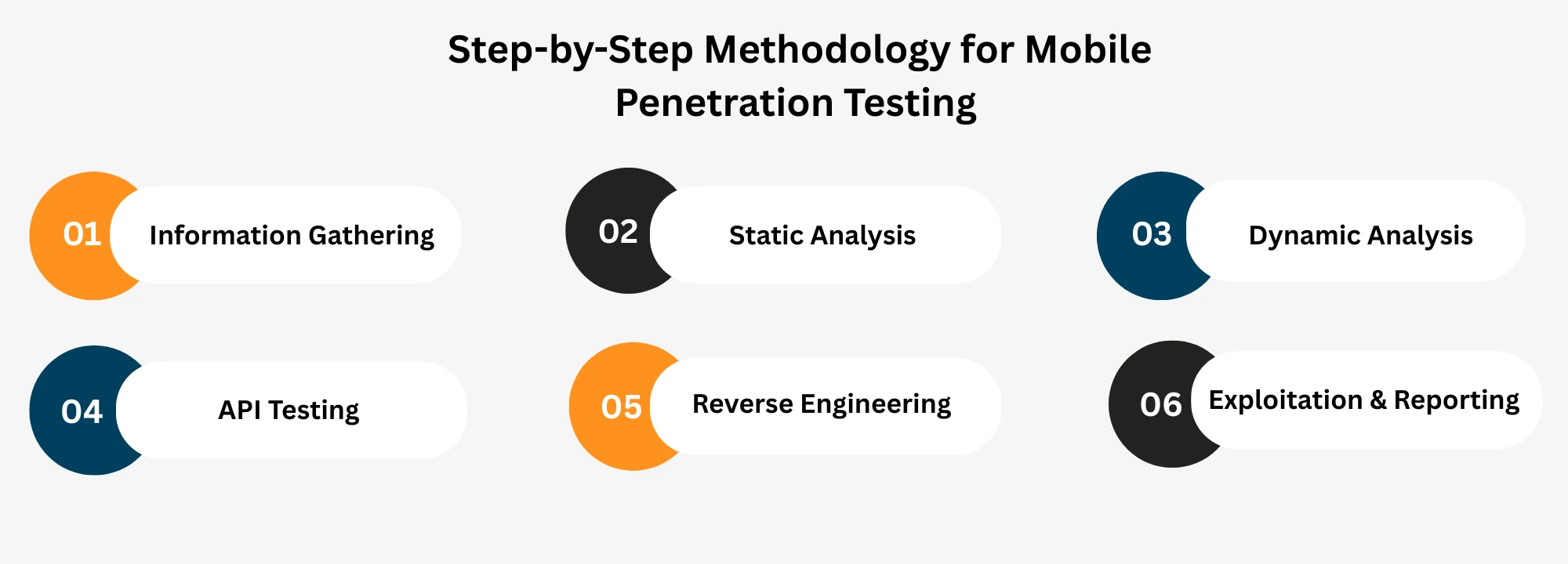
Follow this structured approach to effectively test mobile applications:
- Information Gathering
Collect relevant details, including APK (Android) or IPA (iOS) files, permissions, server endpoints, third-party libraries, and backend APIs.
- Static Analysis
Inspect source code or decompiled binaries using tools like MobSF and JADX to identify coding flaws, insecure cryptography, or improper API usage.
- Dynamic Analysis
Use runtime tools such as Frida and Burp Suite to intercept traffic, observing behavior, and detecting real-time vulnerabilities.
- API Testing
Assess backend APIs for authentication issues, missing rate limits, and vulnerabilities like SQL injections. Tools like Postman facilitate detailed API testing.
- Reverse Engineering
Leverage decompilation tools like APKTool and JADX to inspect proprietary logic and identify vulnerabilities.
- Exploitation & Reporting
Safely exploit identified vulnerabilities to illustrate real-world impacts and document comprehensive remediation strategies.
Tools for Effective Mobile Penetration Testing
| Tool | Platform | Use Case | Free / Paid |
|---|---|---|---|
| MobSF | Android / iOS | Static & Dynamic Analysis | Free |
| JADX | Android | Reverse Engineering APKs | Free |
| Frida / Objection | Android / iOS | Runtime Instrumentation & Bypasses | Free |
| APKTool | Android | Decompiling & Rebuilding APKs | Free |
| Hopper / Class-Dump | iOS | Reverse Engineering iOS Binaries | Paid |
| Burp Suite (Mobile Integration) | Android / iOS | Proxy API Traffic, Fuzzing | Free Paid |
| NowSecure | Android / iOS | CI/CD Integrated Testing | Paid |
| Appknox | Android / iOS | Automated SAST / DAST for Mobile | Paid |
| Zimperium | Android / iOS | Mobile Threat Defense | Paid |
2026 Mobile Threat Watchlist
Stay alert to these emerging threats:
- Fake-App Statistics: Monitor the increasing prevalence of fake apps infiltrating app stores
- SDK Poisoning: Audit third-party SDKs regularly to prevent vulnerabilities from compromised sources
- AI Malware: Adaptive threats built with artificial intelligence
- Mandatory Pinning Controls: Enforce SSL/TLS certificate pinning to secure communication against interception and manipulation
Best Practices for Mobile Penetration Testing
- Always conduct testing in sandboxed devices or emulators and use both rooted/jailbroken and stock devices to simulate real attack scenarios.
- Use static analysis to detect insecure code, hardcoded keys, or weak cryptography, and dynamic analysis to observe how the app behaves at runtime.
- Since most mobile apps depend heavily on backend APIs, focus on authentication, authorization, rate limiting, and data exposure.
- Validate how sensitive data is stored; use Android Keystore or iOS Keychain, never plaintext files or insecure local databases.
- Confirm strong TLS configurations, certificate pinning, and resistance to man-in-the-middle (MITM) attacks.
- Audit SDKs and libraries to ensure they are trusted and up to date, reducing supply chain risks.
- After fixes are applied, retest to confirm vulnerabilities are closed and no regressions are introduced.
- Automate security testing with CI/CD pipelines so vulnerabilities are caught before deployment.
Compliance & Security Frameworks
Ensure compliance with critical security standards:
- HIPAA: For healthcare apps handling Protected Health Information (PHI).
- PCI-DSS: For apps processing credit card data.
- ISO/IEC 27001: Structured security risk management.
- OWASP MASVS: Comprehensive mobile security verification.
- NIST SP 800-163: Guidelines for federal mobile app security.
Conclusion: Embracing Zero-Trust for Mobile
Adopting a zero-trust security model has become essential. Zero-Trust requires continuous verification and limited access, significantly reducing breaches from compromised mobile devices or apps. Regular penetration testing, adherence to best practices, and robust compliance ensure strong, resilient mobile security in 2026.
Take Action Now! Download our Mobile Pen Testing Checklist
Need expert guidance on penetration testing or compliance? Contact us to book a mobile zero-trust readiness call today!
Other Popular Articles
In the digital age, businesses must adopt an ad
GRC is the capability, or integrated collection