What AS4 Actually Solves: Real Outcomes Companies See After Migration
Contributors

Most of the conversation around AS4 focuses on what goes wrong if you don't migrate. This one is about what goes right when you do.
There's no shortage of content about the risks of legacy EDI. And those risks are real. If your team is past the “why” and into the “what’s in it for us,” here are the outcomes of switching.
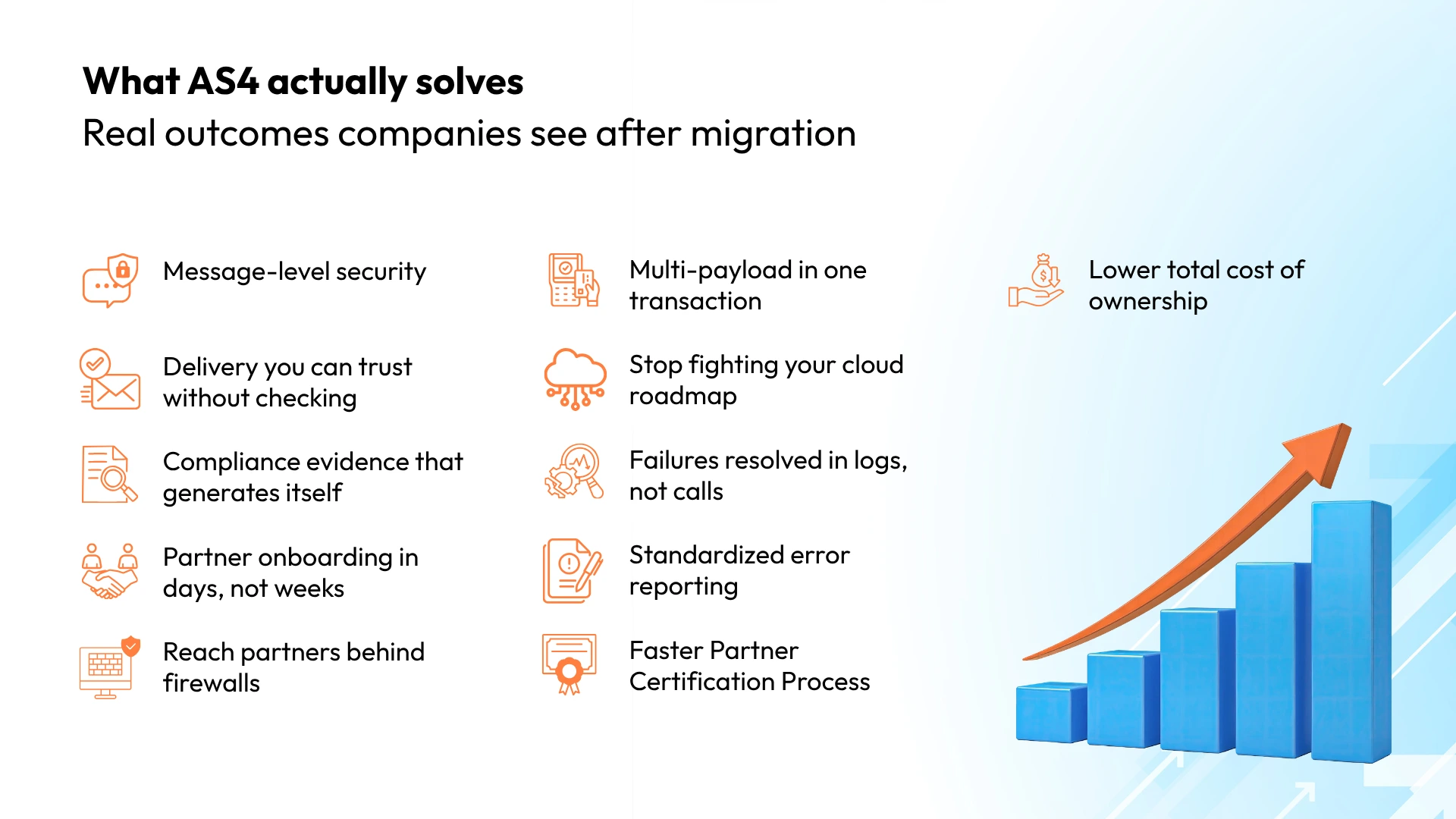
Message-level security
AS2 encrypts the connection. AS4 encrypts the message itself using WS-Security with XML digital signatures. Protection travels with the payload, even through intermediaries or queues. The specific recipient received the specific content intact, as evidenced by the signed SOAP (Simple Object Access Protocol) receipts. In an environment where supply chain attacks doubled in 2025, message-level security is the new baseline.
Delivery you can trust without checking
No more reconciliation reports or follow-up workflows to confirm transactions completed. AS4's built-in duplicate detection, delivery receipts with specific error codes, and automatic retry logic mean your operations team can trust the transport layer without building a second verification layer on top.
Compliance evidence that generates itself
Audit prep shouldn't be a multi-week scramble. AS4 produces digitally signed receipts, sender/receiver verification, timestamps, payload hashes, and delivery confirmation automatically with every transaction. When an auditor asks for proof, the answer is already in the system. No assembling. No chasing logs.
Partner onboarding in days, not weeks
Legacy onboarding means weeks of custom configuration, firewall changes, certificate exchanges, and testing calls for every new partner. AS4 standardizes the handshake through Processing Mode Agreements (PModes), turning a multi-week project into a days-long configuration task. For companies adding ten or more partners a year, this single outcome often pays for the migration.
Multi-payload support in a single transaction
AS2 sends one payload per transaction. AS4 can bundle multiple business documents, attachments, and supporting files into a single message. An invoice with backup documentation. A purchase order with spec sheets. A shipment notice with customs paperwork. Instead of splitting, sequencing, and reassembling related documents across multiple transactions, everything travels together. Fewer transactions, fewer failure points, simpler reconciliation.
Reach partners behind firewalls
AS2 requires the receiver to expose a publicly accessible endpoint at all times. AS4 supports pull mode, where the receiving partner requests messages on their schedule. This opens the door to smaller trading partners who can't or won't expose a public endpoint and to organizations with strict firewall policies. It expands your connected partner network without compromising network security.
Stop fighting your cloud roadmap
Legacy transports require middleware bridges, custom adapters, and translation layers to talk to modern systems. Every one of those is a maintenance burden and a failure point. AS4's SOAP-based architecture integrates natively with API gateways, cloud messaging, and event-driven systems. Your next cloud initiative won't need a side project to work around B2B transport.
Failures resolved in logs, not on calls
Today, tracing a failed transaction means pulling fragmented logs, matching timestamps manually, and calling your partner to compare notes. AS4 gives every message a unique MessageID, signed receipts that confirm exactly what was delivered, and structured metadata tying transport events to business documents. Root cause analysis goes from hours to minutes.
Standardized error reporting
Legacy protocols fail silently or return generic errors that require human interpretation. AS4 defines specific, standardized error signals: authentication failure, decompression error, duplicate message, and receipt timeout. Both partners see the same error language regardless of what platform they're running. Issues get identified and categorized immediately instead of turning into back-and-forth troubleshooting calls.
Faster certification
When a major customer standardizes on AS4 or a compliance framework mandates eDelivery, the question is simple: are you ready or scrambling? Organizations already on AS4 certify in days, not months, and demonstrate integration capabilities that differentiate them from competitors still on legacy stacks.
Lower total cost of ownership
Migration has an upfront cost. But legacy EDI carries hidden ongoing costs: manual troubleshooting, onboarding labor, audit prep, middleware maintenance, and IT staff tied to workarounds instead of strategic work. After migration, those costs drop or disappear. Organizations that consistently track the numbers find that AS4 pays for itself within two years.
The Bigger Picture
These aren't theoretical benefits. They're operational outcomes that show up within months of migration.
- Stronger security from day one
- Reliable delivery without manual checks
- Compliance evidence on autopilot
- Faster partner connections
- A modern stack that doesn't fight itself
- Competitive positioning that wins the next big partner conversation
If you are planning a migration or evaluating your next step, do not rely on guesswork. Join our live webinar below for practical AS4 migration insights, common mistakes to avoid, and strategies you can act on immediately.
Other Popular Articles
In the digital age, businesses must adopt an ad
GRC is the capability, or integrated collection