OT Ransomware Prevention: Practical Best Practices for Industrial Cybersecurity

Ransomware incidents targeting OT/ICS environments escalated in 2025, with attackers using sophisticated evasion in malware like FrostyGoop and IOCONTROL via Modbus/MQTT protocols. Manufacturing faced heavy hits, as perimeter vulnerabilities enabled pivots from IT to OT, causing extended outages.
If you are responsible for operational technology security, you are not protecting data. You are protecting production, safety, revenue, and brand credibility.
This blog breaks down what prevents OT ransomware and where most organizations fail.
Why OT Ransomware Is Different from IT Ransomware
Most prevention failures begin with a wrong assumption.
OT is not IT.
| In IT: | In OT: |
|---|---|
| Systems can be patched weekly. Reboots are acceptable. Downtime is inconvenient. | Downtime costs millions per hour. Safety systems cannot be casually restarted. Legacy devices cannot support modern agents. Patching cycles may require scheduled shutdowns. |
Applying IT playbooks to OT environments creates blind spots attackers' exploit.
If your ransomware defense strategy does not account for uptime constraints, deterministic traffic, and safety interdependencies, it is incomplete.
How Modern OT Ransomware Attacks Actually Happen
Typical attack path:
- Phishing or credential compromise in IT.
- Lateral movement to Active Directory.
- Discovery of VPN or jump host into OT.
- Pivot into the plant network.
- Disable backups.
- Encrypt IT systems first.
- Disrupt operations to increase leverage.
If there are no strict boundaries between IT and OT, ransomware does not require a zero day. It needs poor architecture.
Core OT Ransomware Prevention Best Practices
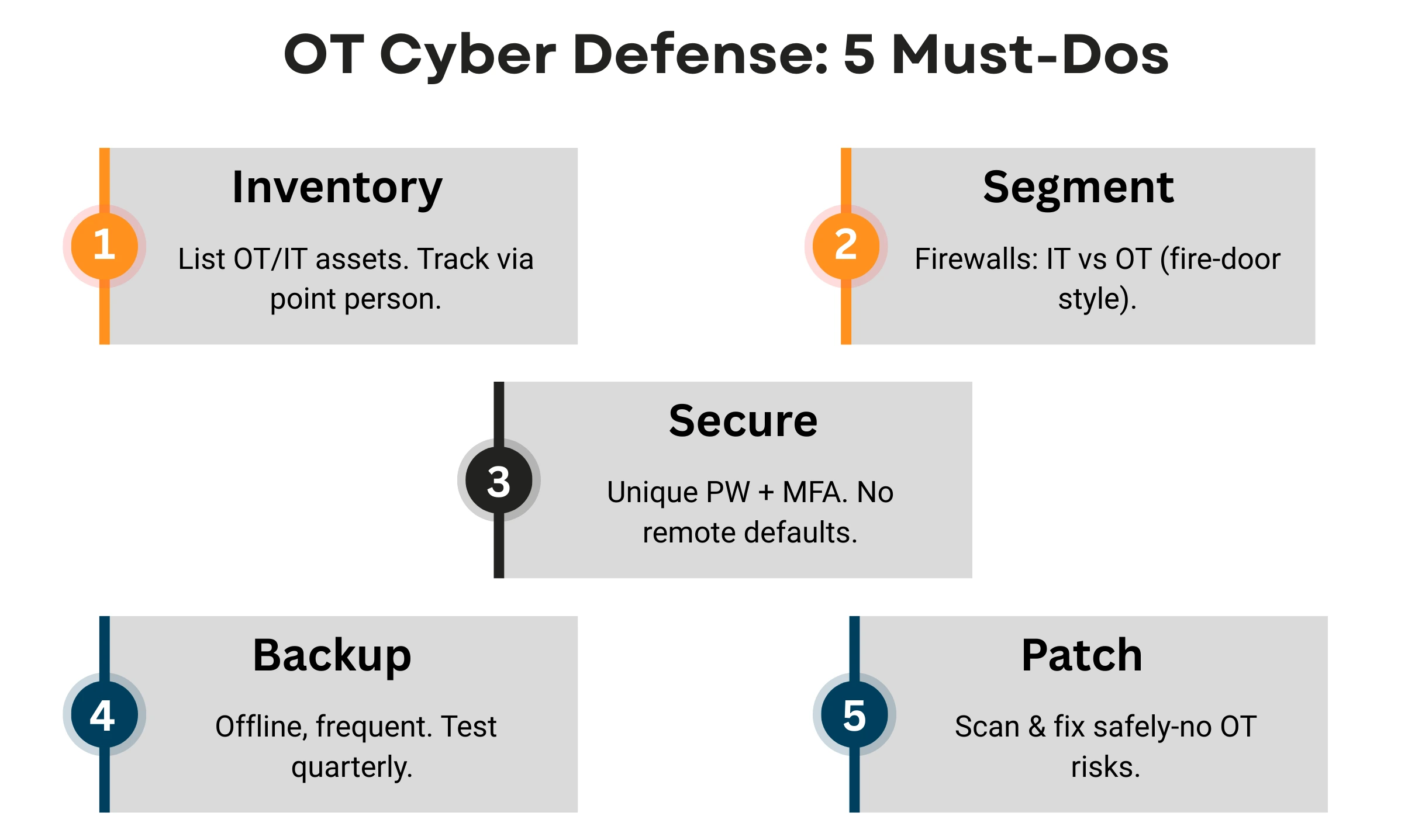
- Inventory Assets: List all OT devices, software, and IT connections; designate a cybersecurity point person to track changes.
- Segment Networks: Use firewalls to separate IT from OT zones, preventing lateral spread like containing a fire in one room.
- Secure Access: Enforce strong, unique passwords (no defaults) and multi-factor authentication (MFA), and limit remote logins.
- Backup Religiously: Maintain frequent, offline/air-gapped backups of critical data; test restores quarterly to ensure usability.
- Patch Vulnerabilities: Scan for known flaws in commodity systems; apply updates where safe without risking OT stability.
Foundational Best Practices Are Only the Starting Point
Reading best practices is easy. Operationalizing them in a live OT environment is complex.
Real prevention requires:
- Detailed architecture models.
- Implementation checklists.
- Configuration examples.
- Defined ownership across teams.
- Tested recovery procedures.
- That is where most organizations stall.
For organizations seeking to move beyond baseline controls and toward measurable resilience, the following advanced OT ransomware defense practices provide a deeper framework for evaluation and strengthening. Access Advanced OT Defense Strategies
Other Popular Articles
In the digital age, businesses must adopt an ad
GRC is the capability, or integrated collection












